
Detecting Exploitation: How Network Monitoring Complements your Security Stack
Summary
Read the Original Article
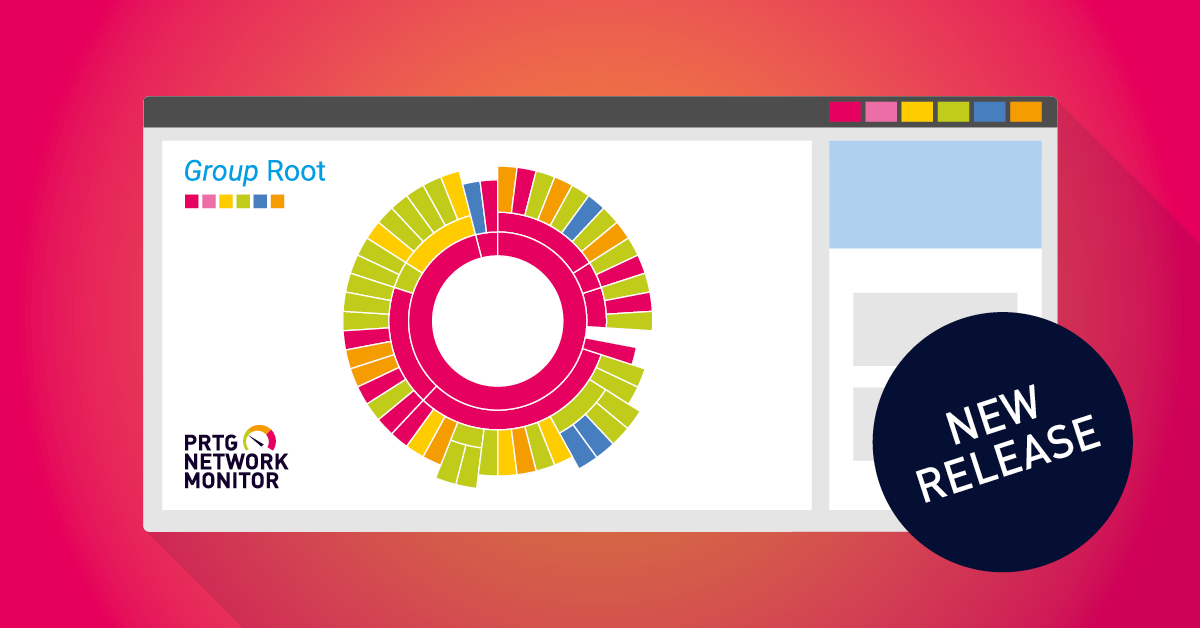
This article originally appeared on Paessler Blog (English).
Read Full Article on Original Site
This article originally appeared on Paessler Blog (English).
Read Full Article on Original Site
Rakesh Shah • Jun 5, 2026
Bryan Patton • May 14, 2026

Ivanti Blog • May 13, 2026

Narayan Annamalai • May 5, 2026

Bastiaan Verdonk • Apr 30, 2026
michael.becker@paessler.com (Michael Becker) • Dec 8, 2025 • 74 views

Michael Becker • Apr 15, 2026 • 72 views
Michael Becker • Apr 10, 2026 • 58 views
Sascha Neumeier • Apr 22, 2026 • 53 views

Michael Becker • Mar 25, 2026 • 53 views